Apple's Quick Look Is a Privacy Fail for Encrypted Files
Even if you encrypt a hard drive connected to your Mac, Apple is (possibly unintentionally) undermining your efforts. This happens as a newly publicized, but long implemented, system feature is quietly creating unencrypted versions of those files, which an informed snooper could view.
While there's no big fix for the issue, we've got instructions for how to clear those data-leaking files from your system.
This month, a pair of security experts, Patrick Wardle and Wojciech Regua, explained on their own blogs how the flaw came out of a simple, seemingly innocuous OS X/macOS function. Quick Look allows you to preview any file on a Mac by selecting it and hitting the Space bar.
MORE: Why I'm Ditching My MacBook Pro for the MateBook X Pro
In his explanation, Regula shows how Quick Look creates a smaller, still legible, version of each previewed file. You don't even need to manually use Quick Look, though. Wardle, who incorporated Regula's own blog posting into his own, showed that the thumbnail of an encrypted text file will reveal at least the first line of text.
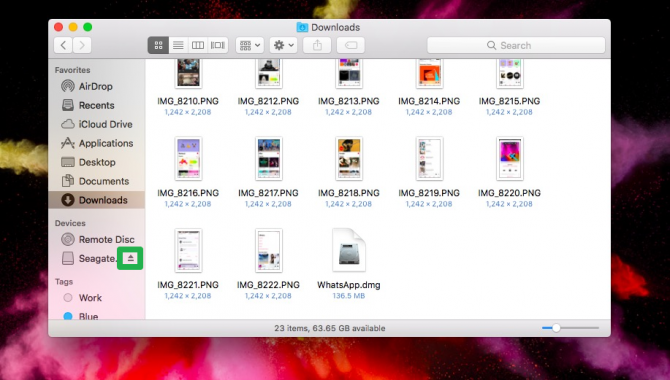
Wardle also found that plugging an encrypted USB drive to your PC will create readable files in the directory that Quick Look uses as a repository on the main, unencrypted hard drive. You don't even have to open the USB drive in Finder, or preview its contents. Anyone who got access to the machine could view the file list of the unencrypted USB drive, even after it had been unplugged.
What to do
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
For now, all you can do is erase the thumbnails that have been created, because macOS doesn't provide an option to end this behavior. Hopefully, Apple will change the way Finder operates so that it stops creating these privacy leaks.
Note: your system will reboot once you finish these steps.
1. Eject the encrypted drive(s).
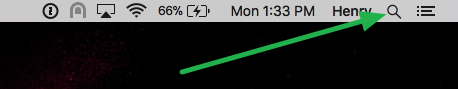
2. Click the Spotlight icon.
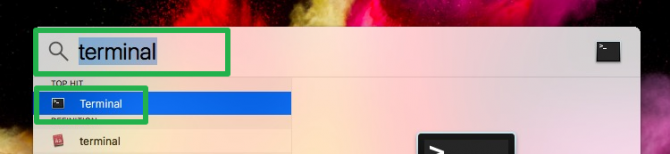
3. Type 'terminal' and open Terminal.
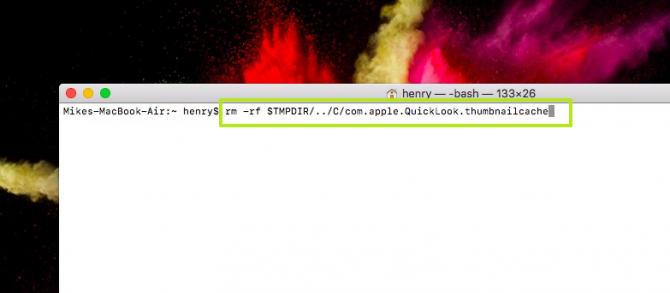
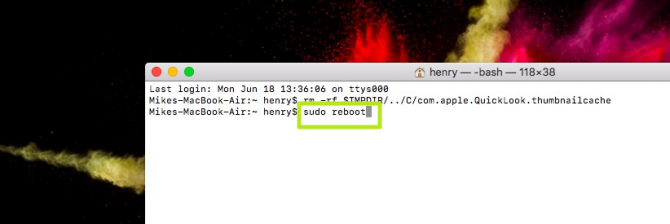
4. Paste in the below text and hit enter.
rm -rf $TMPDIR/../C/com.apple.QuickLook.thumbnailcache
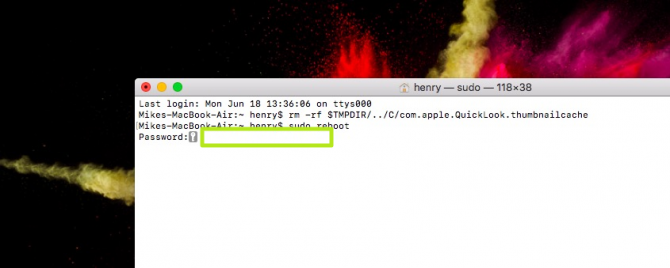
5. Paste in the below test — which will lead to your system resetting — and hit enter.
sudo reboot
6. Enter your password and hit Return.
This isn't exactly new
This problem has cropped up before, even if it hasn't been widely publicized. A 2010 article in OSXDaily.com explained the problem, although that piece assumed that the user would have to preview the file for a thumbnail to be created.
Regula said that viewing cached thumbnails is apparently a known technique among forensic examiners, even though he didn't know about it before. It could be used to help determine the contents of encrypted files and folders created by a person who was trying to stay private.
We've reached out to Apple for comment, and will update this story when we receive a response.
Credit: Ink Drop / Shutterstock
macOS Guide
- How to Password Protect a Folder in a Mac
- How to Force Quit or Close Frozen Applications
- Move Your Mac files to a Windows PC
- How to Dual-Boot Windows and macOS
- Increase the Text Size on Your Mac
- Install or Uninstall Mac Apps
- How to Eject USB Devices and Memory Cards in macOS
- Switch Between Open Apps in macOS
- How to Unlock a MacBook with Your Apple Watch
- Clean Out Your macOS LaunchPad
- How to Use Trackpad Gestures to Navigate macOS
- How to Use Right-Click in macOS
- Use Siri on Your Mac
- How to Customize the Notification Center
- Add a Signature to PDFs with Mac Preview
- Use Memories in the Photos App on Mac
- How to Use Night Shift in macOS
- How to Change Your Mac's Password
- How to Edit Siri's Activation Keyboard Shortcuts on macOS
- Change Views in Finder
- Use macOS Dark Mode
- Transfer Files with AirDrop
- How to Use Mission Control on a Mac
- Use Optimized Storage
- How to Enable Parental Controls on a Mac
- How to Mark Up PDFs in macOS
- Back Up Mac with Time Machine
- How to Use Dictation on a Mac
- How to Use the macOS Feature
- Use Apple Pay in macOS
- How to Block Websites on Your Mac
Henry was a contributing writer at Laptop Mag. He penned hundreds of articles, including helpful how-tos for Windows, Mac, and Gmail. Henry has also written about some of the best Chromebooks, and he has reviewed many Apple devices, including various MacBook Air laptops. He is now a managing editor at our sister site Tom's Guide, covering streaming media, laptops, and all things Apple.