What is TPM 2.0 — the chip you need to run Windows 11
Here's why TPM chips are a requirement for Windows 11

PC makers often list a Trusted Platform Module (TPM) as a security feature for laptops and desktops and TPM 2.0 will be a system requirement for Windows 11, but you may not know what it is or why it's useful. Primarily, the TPM enhances security above and beyond the capabilities of consumer software. It also can be used to keep your PC running well.
Since an industry consortium called the Trusted Computing Group (TCG) introduced TPM in 2009, more than 2 billion of the chips have been embedded into PCs and other devices, such as ATMs and set-top boxes. The TPM standard has been updated over the years, and its most recent release is TPM 2.0, which was released in October 2014.
- Windows 11 revealed — all the changes coming to Microsoft's next-gen Windows OS
- Best laptops 2021
- Windows 11 tip: How to enable TPM 2.0 in BIOS
What is a TPM?
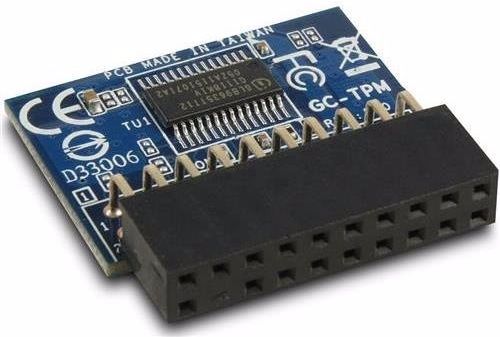
A Trusted Platform Module is a microchip that is often built into a computer to provide hardware-based security. It can be added later by industrious users who attach the chip to the motherboard. Not all motherboards offer a TPM connector, so you'll need to research your model first.
What does a TPM do?
Some, but not all, of the data we transmit throughout the day is sent unencrypted, as plain text. TPM chips use a mix of software and hardware to protect any important passwords or encryption keys when they are sent in this unencrypted form.
If a TPM chip senses that a system's integrity has been compromised by a virus or malware, it can start up in a quarantine mode to help fix the problem. Some Google Chromebooks include TPMs, and during startup, the chip scans the BIOS (a motherboard firmware that initiates the startup process) for unauthorized changes.
TPM chips also provide safe storage of encryption keys, certificates and passwords used for logging in to online services, which is a more secure method than storing them inside software on the hard drive.
TPM chips in network-connected set-top boxes enable digital rights management, so media companies can distribute content without worrying about theft.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
Who is TPM for?
While originally targeted at enterprises or larger companies looking to secure their data, TPM chips are now becoming a requirement for all laptops and desktops to ensure security for all users.
Microsoft announced that Windows 11 will make TPM 2.0 a requirement, this shouldn't present an issue for most users as it has been present on laptops and CPUs since around 2016, but some will need to either update their hardware or upgrade to a new laptop if they want to make the switch to Windows 11.
How do you use a TPM?
If you buy a PC with a TPM chip, you can enable its encryption to protect your data by accessing the BIOS. IT departments often manage TPM chips in enterprise devices.
Major notebook makers — including Dell, HP and Lenovo — often include software applications that will help users access TPM features.
What can you do with a TPM?
The most basic use for a TPM is to set a login password for your system. The chip will automatically guard that data, rather than keep it stored on your hard drive. If a system has a TPM chip, its user can generate and manage cryptographic keys used to lock the system or specific files.
Many people use a TPM to enable Windows' BitLocker Drive encryption utility. When you power up a system that features a TPM and BitLocker, the chip runs a series of conditional tests to see if it's safe to boot up. If a TPM senses the hard disk was moved to another location, as might be the case if it were stolen, it locks the system.
Notebooks with built-in fingerprint readers often keep the recorded fingerprints in the TPM, as its security makes it a responsible location for storage. The chip also enables smart-card readers, which certain companies require for user authentication and login.
Henry was a contributing writer at Laptop Mag. He penned hundreds of articles, including helpful how-tos for Windows, Mac, and Gmail. Henry has also written about some of the best Chromebooks, and he has reviewed many Apple devices, including various MacBook Air laptops. He is now a managing editor at our sister site Tom's Guide, covering streaming media, laptops, and all things Apple.