LeapFrog Tablet May Fall for Easy Hacks
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
You are now subscribed
Your newsletter sign-up was successful
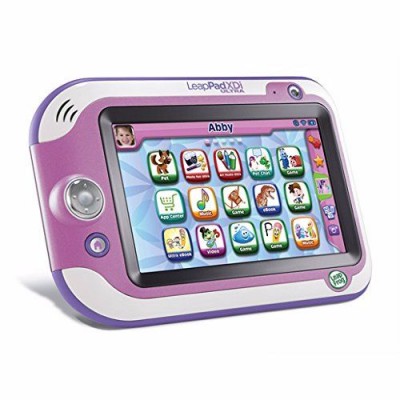
While it’s possible to overstate the danger hackers pose to kids (grown-ups are generally much more tempting targets), there’s still something insidious about the idea of a cybercriminal targeting younglings through toys. Enter the LeapPad Ultra: a kids’ tablet that’s filled to the brim with educational games, funny videos and, according to one researcher, easily compromised software.
This information comes by way of Offensive Security, an independent security blog run by researcher Mike Carthy. After he and his wife attempted (and failed) to pick up a Wi-Fi enabled Barbie doll, he bought a LeapPad Ultra as a consolation prize. The box advertised “Kid Safe Wi-Fi,” but Carthy found that the gadget offered anything but.
The first thing Carthy found was that the $150 tablet did not offer a firmware update upon starting up. While such a process might be confusing for a preschooler, it also means that the tablet will not run the most up-to-date software out of the box. This is an instant security risk.
Article continues belowThis lack of security extended to the LeapPad Ultra’s online media player, which was actually a Web browser hard-coded to LeapFrog's cloud-content server. Carthy used a networking tool called Wireshark to deduce the IP address of LeapFrog's server, then rerouted the traffic so that the LeapPad connected to Carthy's laptop instead. At best, this means a third party could subject a child to objectionable material; at worst, he or she could infect the system with malware, or phish information from a parent account.
Perhaps the worst problem, Carthy said, was that the LeapPad Ultra used an Adobe Flash Player browser plugin to power its video content. Those of you who have been following Adobe news know that Flash Player can be notoriously insecure, and that the only way to avoid catastrophic security issues is to keep the program aggressively up-to-date.
The LeapPad Ultra does not automatically update Flash Player, or prompt the user to install an update. To be fair, if you set up the device as recommended and install the LeapFrog Connect companion application on your computer, it will update Flash to the current, vulnerability-free version once the LeapPad is connected to a PC or Mac.
However, updating Flash is not necessary to watch Flash videos. If you hand off a LeapPad Ultra to a child before installing LeapPad Connect on your own machine, a hacker could compromise it quite easily with a remote code execution via the Flash flaw. This code could do anything from hijacking the device to drafting it into a botnet.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
“Can you imagine being DDoS’d by a LeapFrog botnet?” McCarthy wrote. “You’d never live something like that down – ever.”
If you buy a LeapPad Ultra, be sure to install the Connect companion software as soon as possible and keep the device up to date — although that will only mitigate its security problems, not solve them entirely. Granted, it’s questionable how much damage a hacker could (or would want to) do with a tablet for small children, but chances are, someone’s willing to try.
UPDATE: LeapFrog rejects some of the assertions in Carthy's blog post, specifically regarding the usage of Flash on the LeapPad Ultra.
"Adobe Flash use on the device is for games available on the device only," read a statement provided by a LeapFrog spokesperson. "It is not used in any process which would connect to the Internet."
"The LeapSearch embedded browser does not use Adobe Flash and utilizes the more secure HTML5," the statement said. "We find the statements in Mr. Carthy's article to be false."