Hackers Locking, Ransoming Macs: How to Protect Yourself
Apple users: If you haven't made your iCloud password strong and unique, today might be a great day to do so.
We're seeing reports of online ne'er-do-wells taking advantage of a long-existing system-locking tool in iCloud's Find My Mac feature, which isn't locked behind two-factor authentication, to lock up Macs remotely and hold them for ransom.
These reports, first seen by MacRumors, came from Twitter users including @bunandsomesauce. He posted evidence of the lock of his Mac with a photo of the ransom note on his Mac's screen, asking for $50 in Bitcoin. Another Twitter user, @jcaffoe, lost access to his Mac, and he's worried that he won't get it fixed any time soon because his local Genius Bars are booked solid for a week.
So a hacker gained access to my iCloud account (despite two-factor authorization) while I was asleep this morning. — Jason Caffoe (@jcaffoe) September 20, 2017
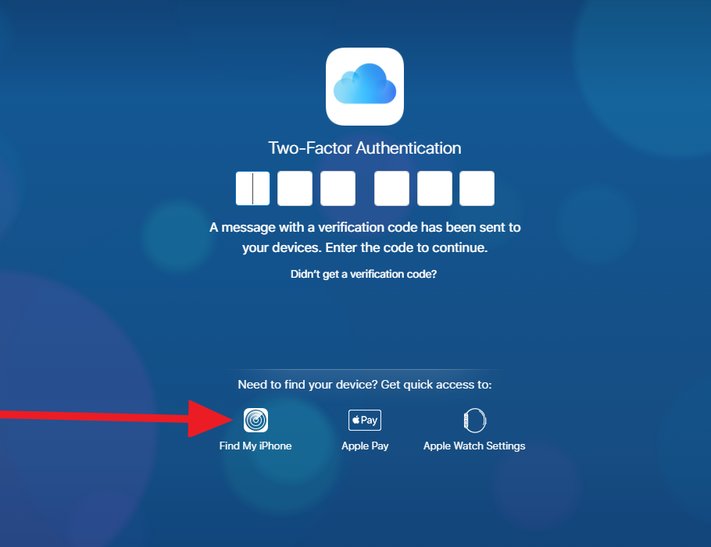
These attacks aren't due to a mistake, or a change in how Apple implements two-factor authentication (2FA). The company intentionally makes its Find My iOS and macOS device services — which can place a lock-code on a machine — accessible once you've entered your iCloud password.
The reasoning is because you might have lost access to your trusted device as a result of the theft (your iPhone, for example, could be stolen from you in public). We've argued in the past that Apple needs to find some way to implement 2FA for this service, but to no avail.
Such remote takeovers have plagued iPhone users for years. But now that Apple has extended the same "Find My Device" service to Macs, online criminals are using the same technique to hijack laptops and desktop computers.
What should you do?
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
First of all, never recycle your passwords for important accounts such as online banking, Google, email services, social networks, or your Apple account. All should be protected by strong, unique passwords.
But a unique password isn't exactly enough. Make sure it's long and extremely difficult to guess, which disqualifies your mother's maiden name, your birthday, Social Security number or your pet's name.
Y'all my MacBook been locked and hacked. Someone help me @apple @AppleSupport pic.twitter.com/BE110TMgSv — Jovan (@bunandsomesauce) September 16, 2017
Breaches of online services servers include the theft of passwords, and they happen increasingly often these days. This results in data dumps existing online that contain troves of email address and password combinations, just waiting to be tested to see if they work for iCloud and other services.
Another common way to get passwords is through phishing attacks. Because of the high value of a stolen Apple account, Mac and iPhone users are frequently lured to fake Apple login pages that may look very much like the real thing.
And if you're already hit?
It's time to contact Apple Support to prove your identity and get their help in unlocking your machine. Click here to see if your local Genius Bar is accepting appointments today or start a chat or phone call with a rep.
Apple Laptop Guide
Henry was a contributing writer at Laptop Mag. He penned hundreds of articles, including helpful how-tos for Windows, Mac, and Gmail. Henry has also written about some of the best Chromebooks, and he has reviewed many Apple devices, including various MacBook Air laptops. He is now a managing editor at our sister site Tom's Guide, covering streaming media, laptops, and all things Apple.