Microsoft warns of 'massive' COVID-19 email phishing campaign: What to do
Here's how to spot the phishing emails

Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
You are now subscribed
Your newsletter sign-up was successful
If you receive an email claiming to show a COVID-19 "Situation report" from Johns Hopkins Center, don't click on it.
Microsoft has put out a warning against a "massive" phishing campaign that tries to trick people into opening email attachments containing malicious Excel 4.0 macros. The campaign, which started on May 12, uses COVID-19 news as a lure to get people to open an email and download infected attachments. Microsoft wrote in a Twitter thread that the attackers have used "several hundreds" of unique attachments.
- Windows 10 update is wrecking laptops — now Microsoft is investigating
- Best business laptops in 2020
- Google Chrome update beefs up online security and privacy measures
The phishing emails claim to come from Johns Hopkins Center and contain the subject line "WHO COVID-19 SITUATION REPORT." Don't open this email. If you do, and you opened the attached Excel files, you'll see a security warning before a graph of US coronavirus cases appears.
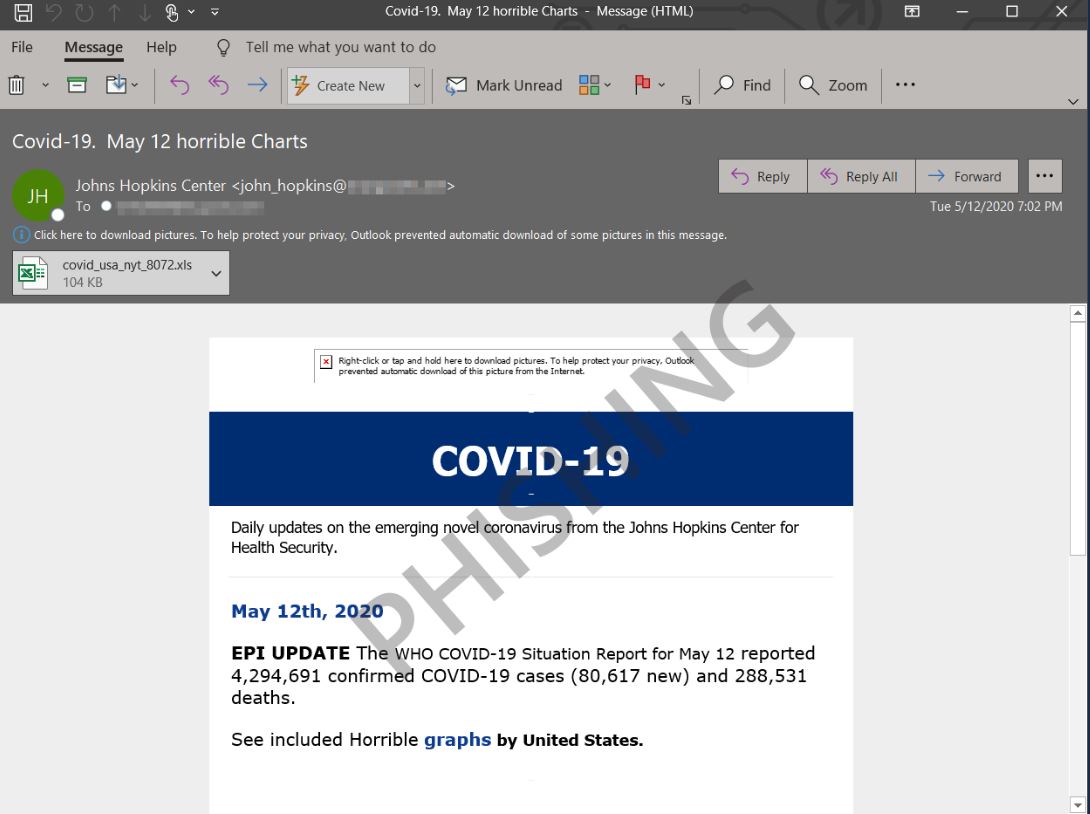
You might think you're in the clear, except that while you're looking at the data, a malicious Excel 4.0 macro downloads in the background and runs NetSupport Manager RAT, a remote access tool often misused by cybercriminals to gain access to computers. Worst yet, the NetSupport RAT unloads more components that connect to a C2 server and gives attackers the ability to send further commands.
Phishing campaigns are increasing in frequency as remote work becomes more common during the COVID-19 pandemic.
"For several months now, we’ve been seeing a steady increase in the use of malicious Excel 4.0 macros in malware campaigns," Microsoft's Security Intelligence team tweeted. "In April, these Excel 4.0 campaigns jumped on the bandwagon and started using COVID-19 themed lures."
What to do
Be extra cautious when opening emails from an unknown sender. Even if an email domain looks legit, it's always a good idea to do a Google search to see if others have flagged it as a phishing attempt.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
The Federal Trade Commission has some useful tips on how to spot a phishing campaign and avoid opening malicious links. We recommend visiting the FTC website and familiarizing yourself with these guidelines.
You should also download good antivirus software on your laptop or desktop. Antivirus apps will flag phishing sites for you, but don't rely on them to catch everything. Keep in mind that phishing websites can be hard to spot and the more advanced attempts can bypass antivirus detections.
Phillip Tracy is the assistant managing editor at Laptop Mag where he reviews laptops, phones and other gadgets while covering the latest industry news. After graduating with a journalism degree from the University of Texas at Austin, Phillip became a tech reporter at the Daily Dot. There, he wrote reviews for a range of gadgets and covered everything from social media trends to cybersecurity. Prior to that, he wrote for RCR Wireless News covering 5G and IoT. When he's not tinkering with devices, you can find Phillip playing video games, reading, traveling or watching soccer.

