iOS apps found committing ad fraud — delete these iPhone apps before adware attacks
Malicious Android and iOS apps with 13 million downloads spotted committing ad fraud

Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
You are now subscribed
Your newsletter sign-up was successful
iPhone and Android apps with over 13 million downloads have been discovered to be committing different methods of ad fraud, including new adware tactics that allow threat actors to quietly make a profit.
Cybersecurity researchers at Satori Threat Intelligence and Research Team found a collection of apps across the App Store and Google Play Store that contained malicious code, with the ad fraud operation being dubbed "Scylla." Satori worked with Apple and Google security teams to remove the iOS and Android apps in both stores.
According to the report, more than 75 Android apps and 10 iOS apps committed "several different flavors of advertising fraud," letting threat actors pretend these apps are legitimate and make a profit through hidden ads and fake clicks.
This was done through App and bundle ID spoofing. The Scylla apps contain code that lets advertisers and ad tech companies believe these are popular apps. This tricks companies into placing ads and, even worse, spending money to place ads in the app — especially if it's a gaming app or streaming service.
The malicious apps also use adware tactics by using hidden ads the user can't see and having ads pop up even when the app isn't open. By having these ads pop up and users accidentally click on them, the threat actors make a profit.
The Scylla apps also used code to garner fake clicks on ads so advertising companies think they are being clicked on. Clicks are better than views, meaning the fraudsters were gaining extra money from ads that weren't being clicked on.
Scylla stems from a family of ad fraud methods, with the first set of malicious apps being discovered in 2019 by the Satori team. Known as "Poseidon", the scheme saw 40 Andoird apps commit ad fraud, which also used out-of-context and hidden ads. In late 2020 and early 2021, Satori found the second wave of the scheme, which is labeled "Charybdis."
As the report points out, Scylla stands out by targetting advertising SDKs not just for Android apps but also for iOS apps. Apple's App Store is known to have a secure line of defense to avoid malicious apps on its store, but Scylla slipped through with 10 iOS apps.
Delete these iOS apps
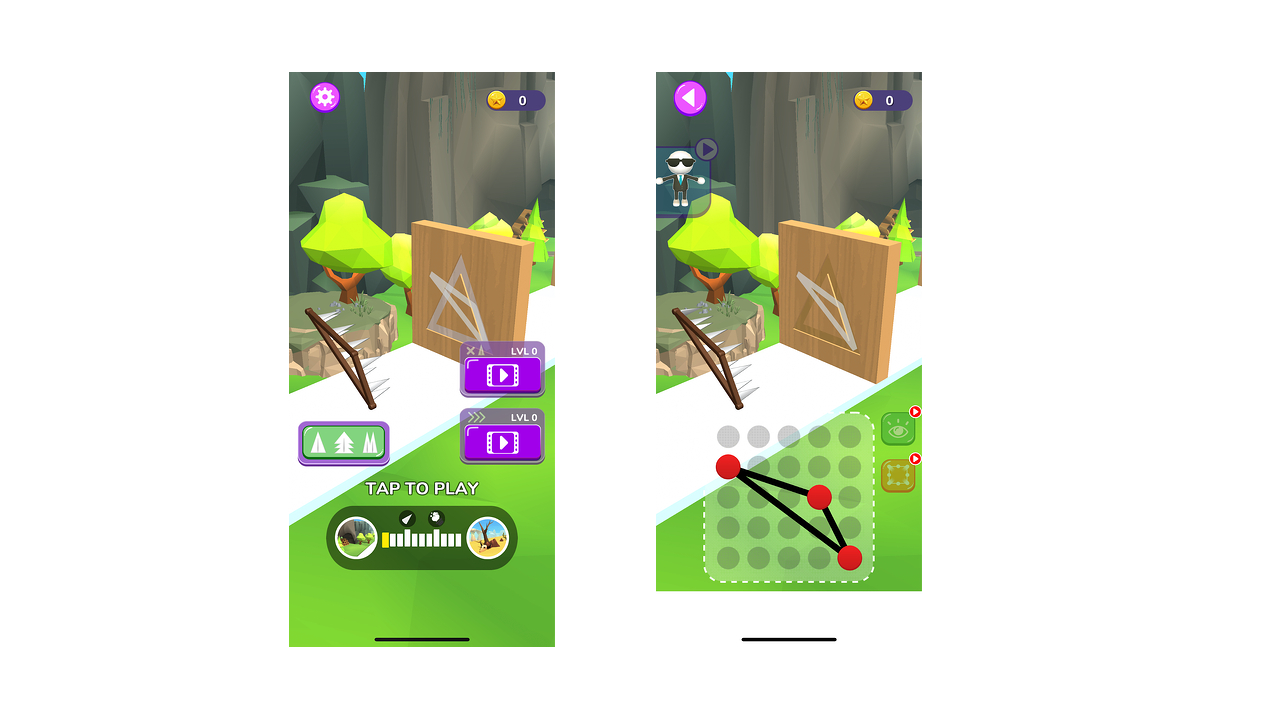
While the Satori team confirms that apps have been taken down on both the App Store and Google Play Store, it's a good idea to see if these apps are still installed on your iPhone. These apps are run-of-the-mill games that you'd typically find on iOS. Here are nine of the known apps:
- Loot the Castle
- Run Bridge
- Shinning Gun
- Racing Legend 3D
- Rope Runner
- Wood Sculptor
- Fire-Wall
- Ninja Critical Hit
- Tony Runs
For a full list of apps both on iOS and Android, check out the full report on HUMAN Security. More apps using the Scylla attack method could pop up, so be sure to keep an eye out for suspicious-looking apps.
Recently, we've seen a new malware that stealing credit card and personal data, along with malware stealing passwords and credit card info. To keep yourself secure, check out the best antivirus apps around, and learn what you need to know about adware, ransomware, and spyware.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.

Darragh Murphy is fascinated by all things bizarre, which usually leads to assorted coverage varying from washing machines designed for AirPods to the mischievous world of cyberattacks. Whether it's connecting Scar from The Lion King to two-factor authentication or turning his love for gadgets into a fabricated rap battle from 8 Mile, he believes there’s always a quirky spin to be made. With a Master’s degree in Magazine Journalism from The University of Sheffield, along with short stints at Kerrang! and Exposed Magazine, Darragh started his career writing about the tech industry at Time Out Dubai and ShortList Dubai, covering everything from the latest iPhone models and Huawei laptops to massive Esports events in the Middle East. Now, he can be found proudly diving into gaming, gadgets, and letting readers know the joys of docking stations for Laptop Mag.