This VPN service uses cryptocurrency to make browsing the internet safer — here’s how
Decentralized VPNs questions if VPN services are worth your trust

A virtual private network’s (VPN) main priority is to keep your data hidden. Giving you access to content around the globe is a fantastic perk, and if it can boost your internet speeds, all the better. Regardless, the best VPN services today do everything they can to make sure you stay anonymous online.
One way these services reassure customers their data is safe is by emphasizing their no-logs policy. This means your VPN provider’s centralized servers don’t collect or keep a digit of data. Or, so these services claim.
More often than not, general VPN users trust their chosen provider because they simply state they have “no logs.” Unless you go out of your way to see these servers yourself, let alone understand what in the world to search for, it’s hard to prove that claim. It all whittles down to this: How do you trust a VPN service?

To get a better idea of how this all works, I spoke to co-founder and CEO of Exidio — the development arm of VPN service Sentinel — Dan Edlebeck. As it turns out, a decentralized VPN (dVPN) is exactly what privacy-conscious VPN users need to prove their data isn’t being logged. In fact, it can even offer cryptocurrency in exchange.
What is a dVPN?
When I asked Edlebeck this question, I must have looked like I did after watching Christopher Nolan’s Tenet for the first (and second) time; dazed and confused. In truth, it isn’t hard to wrap your head around, but I’m still happy he put it in layman’s terms.
“A decentralized VPN (dVPN) is a peer-to-peer network for people to offer and connect to a bandwidth network,” Edlbeck said. “Anyone can offer their excess bandwidth from their home or from a data center, and people can also route their traffic through that excess bandwidth.”
As he puts it, a dVPN is a marketplace where people can offer a decentralized bandwidth via a peer-to-peer network. It’s all managed by whoever wants to opt-in.
“The benefit of using a VPN is really the same as using a centralized VPN or a decentralized VPN. You're using both for the same use cases, but in a decentralized architecture, it's individuals that are offering the nodes on the network.” Exidio, or any other company for that matter, has no way of accessing the traffic. Those who host the node can’t view a user's private information or metadata, either.

One of the best reasons to use a dVPN is the number of IP addresses from all over the world from different people routing them through their own home internet service provider. Edlebeck offers an example of this: “Even when people use a VPN, they're trying to get access to content and they can't because the IP address that they're using on their VPN has been blacklisted from some site as identified as VPN. With a dVPN, you have a global network of IP addresses and they're not all coming from certain data centres that have been identified as a VPN.”
More importantly, a dVPN is open source. This means users are able to prove web traffic and metadata are end-to-end encrypted. However, you’ll find that the best VPN services only use centralized systems. Naturally, this begs the question...
Can we trust VPN services?
When it comes down to it, no. However, that answer comes with a huge asterix, which Edlebeck breaks down.
When using a VPN, especially at a high level, one of its main use cases is protecting your traffic, information and personal data. Another is accessing internet content you wouldn't otherwise see due to geo-restrictions (a.k.a geo-blocks). This is important. As Edlebeck points out, certain internet service providers can log your metadata and resell it to other parties for their own benefit. It’s nasty business, but business all the same.
That’s when a VPN comes in handy...right? While many VPN companies claim they're not logging user data, these companies aren’t open-source. This means they can’t prove the “no-logging” guarantee — which you’ll often find on VPN service websites — is taking place. Users are taking the company’s word for it.
To help with these claims, companies will have third-party audits so they can validate and assure users there is no logging taking place. ExpressVPN recently used auditing firm PricewaterhouseCoopers (PwC) to confirm the VPN service’s privacy protection, while NordVPN also used PwC to evaluate its no-logs claims. These are two of the biggest VPN providers, so it would be bizarre if they didn’t both ace their evaluations.
However, as Edlebeck points out, “NordVPN, one of the biggest VPN companies in the world, had a data breach in 2019 proving [it was] logging user data.” NordVPN addressed the breach to let users and potential customers alike know its network is still safe to use — emphasizing “the affected server did not contain any user activity logs.”
PwC is one of the biggest auditing firms in the world, and is well regarded as a trustworthy company — its slogan is “to build trust in society and solve important problems.” Gaining assurance from PwC is a good sign for NordVPN, but it takes more than just a guarantee to gain trust. The WhatsApp privacy changes earlier in 2021 are a testament to that.
This is how dVPN services such as Sentinel differ. “There is no one company that can actually track and log your data,” Edlebeck explains. “The front-facing applications (i.e. browser extensions, Android apps) that you're using to connect to the Sentinel network are open source, so you can review the code base and prove that they are end-to-end encrypted.”
What is Sentinel?
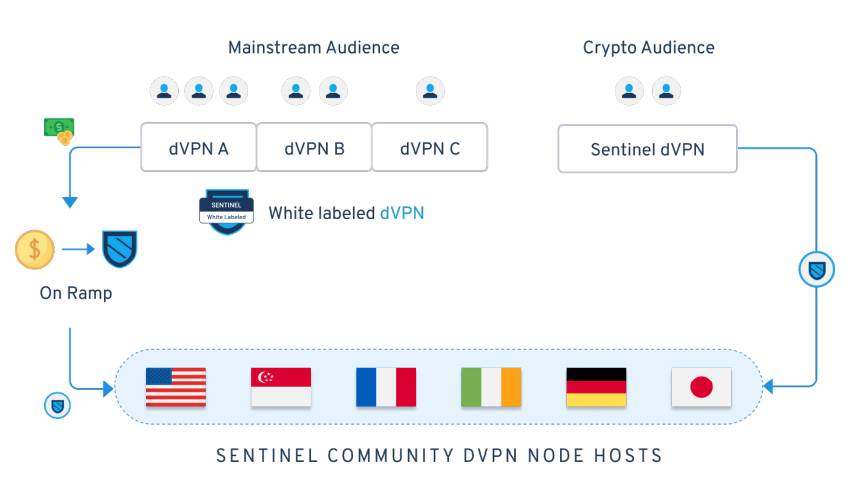
As Edlebeck states, Sentinel is a dVPN peer-to-peer network where anyone can offer and host their bandwidth. Exidio is one of the software development companies building on the Sentinel network, which also works on the application and its user interface.
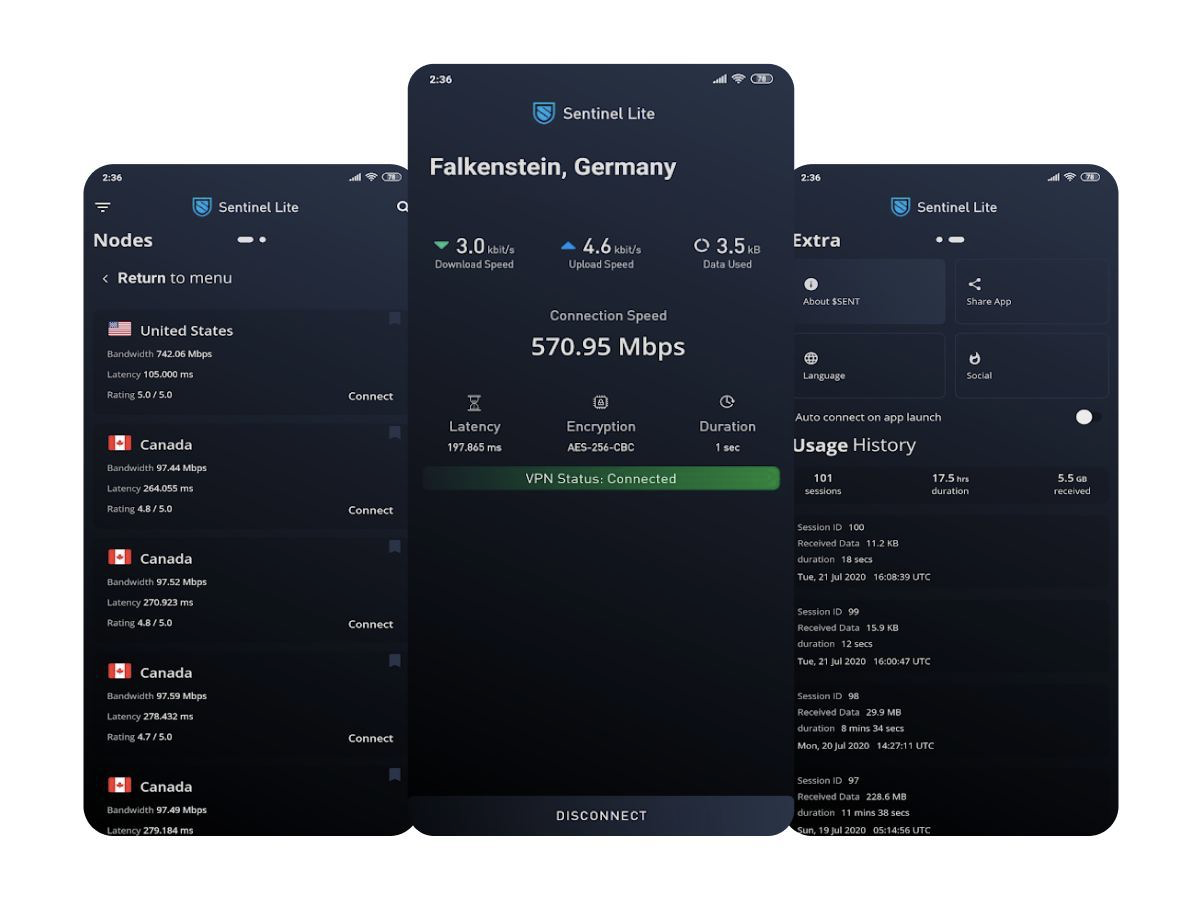
So, while the Sentinel decentralized VPN app is now available on Android via the Google Play Store, this is only the start of something much bigger. “Sentinel isn't one front-facing application. Sentinel is a framework for any company or individual that either already exists as a VPN company or an entrepreneur that wants to start their own application to connect to.”
Exidio is looking to build on its framework to reach the global VPN market. If VPN services really want to prove they are end-to-end encrypted, and not have to rely on their own infrastructure and architecture to start their own company, they could build it on top of the Sentinel network. The more people that join the decentralized network, the more bandwidth available. With bandwidth comes faster internet speed, which is always a plus with any VPN service.
However, how do you make sure users will offer their bandwidth? Well, cryptocurrency is a nice incentive. Edlebeck explains the biggest opportunity to scale the number of people that are offering bandwidth to the network is through monetization. “So, there's kind of two sets of nodes. There are the validator nodes validating the blockchain, and this is pretty common within the crypto industry to secure a blockchain especially within Cosmos. But then, you know, there's the people offering their bandwidth, the decentralized VPN nodes.”

Getting paid to offer bandwidth is a fantastic monetization plan, especially for those familiar with peer-to-peer networks. However, Sentinel currently isn’t monetized yet. Edlebeck explains there is still some work to be done, although there have been “test nets” with “incentivized periods of time” to build the network.
Even better, he continued to say the network will be monetized over the next couple of months. This could bring about a whole new way of using VPN services, especially knowing you can check to see if your data while surfing the web is encrypted.
Is the global VPN market big enough to sustain such a monetized network?
According to Edlebeck, the VPN industry is bigger than ever before. Instead of it originally being an esoteric idea — something only a few people interested in networking would use — VPN services have turned into a “mass consumer adopted product.” He’s right.

In 2016, the VPN market was valued at around $15 billion, which quickly rose to a $30 billion dollar industry in 2020, according to the Exidio CEO. By 2027, it’s expected to be a $107 billion industry, which is a lot more than reported estimates in 2020. “it's growing at a rapid rate, and COVID has only been an extreme accelerant that, as people move online and are used to more remote work, they're looking for secure connections.”
There are many places in the world that now use VPNs out of necessity so they can simply get access to content. For example, trending audio-only app Clubhouse has recently been banned in Oman (via Aljazeera), but a VPN can bypass those restrictions.
While accessing different shows on streaming services like Netflix plays a major part in VPN services becoming a consumer product, Edlebeck mentions there’s another side to it all. “There's more extreme and interesting uses like activists looking to be able to share information in real-time, maybe in a conflict zone. With their internet restricted or content restricted they'll use VPN to be able to share information.”
Outlook
Decentralized VPNs offer a whole new way for VPNs to be used. Eventually, those who adopt it and host nodes can get paid through cryptocurrency for offering their excess bandwidth to others. What’s more, thanks to Exidio, there’s even a way to natively integrate the dVPN framework into existing applications — if these other services are looking for a way to truly claim they have a no-logs policy.
Despite this, will a more consumer-focused VPN market bother to look up “no-logs” themselves? For those who simply want to watch all the anime they can handle on Netflix in Japan, probably not. However, for the high-level VPN users, along with those who might be stuck in heavily censored countries, a dVPN could one day be your best option.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.

Darragh Murphy is fascinated by all things bizarre, which usually leads to assorted coverage varying from washing machines designed for AirPods to the mischievous world of cyberattacks. Whether it's connecting Scar from The Lion King to two-factor authentication or turning his love for gadgets into a fabricated rap battle from 8 Mile, he believes there’s always a quirky spin to be made. With a Master’s degree in Magazine Journalism from The University of Sheffield, along with short stints at Kerrang! and Exposed Magazine, Darragh started his career writing about the tech industry at Time Out Dubai and ShortList Dubai, covering everything from the latest iPhone models and Huawei laptops to massive Esports events in the Middle East. Now, he can be found proudly diving into gaming, gadgets, and letting readers know the joys of docking stations for Laptop Mag.