Microsoft says 99.9% of accounts get hacked for this reason: How to protect yourself
1.2 million Microsoft accounts got hacked in January 2020

It's not us; it's you! Microsoft engineers said at the RSA conference that for 99.9% of hacked accounts, users did not implement multi-step authentication to provide an additional layer of security to ward off cybercriminals, ZDNet reported.
The Redmond-based tech giant revealed that it tracks more than 30 billion log-in events daily and more than one billion active users monthly. On average, 0.5% of Microsoft accounts get compromised per month. To put that statistic into perspective, that's a whopping 1.2 million accounts every 30 days or so.
- Microsoft might rename Cortana — and you won't like it
- Windows 10 Microsoft account enforcement is expanding — and people are angry
- Windows 10 update causes PCs to crash — Microsoft says everything is fine
"If you have an organization that has 10,000 users, 50 of them are going to be compromised this month," said Alex Weinert, Microsoft's director of identity security.
Weinert zoomed in on Microsoft enterprise accounts, and noted that only 11% enabled a multi-factor authentication solution. Weinert said that multi-step authentication is crucial because it would increase data protection against hackers' preferred method for infiltrating Microsoft accounts, which is password spraying.
Password spraying, according to ZDNet, is "a technique during which an attacker picks a common and easy-to-guess password, and goes through a long list of usernames until they get a hit and can access an account using said password."
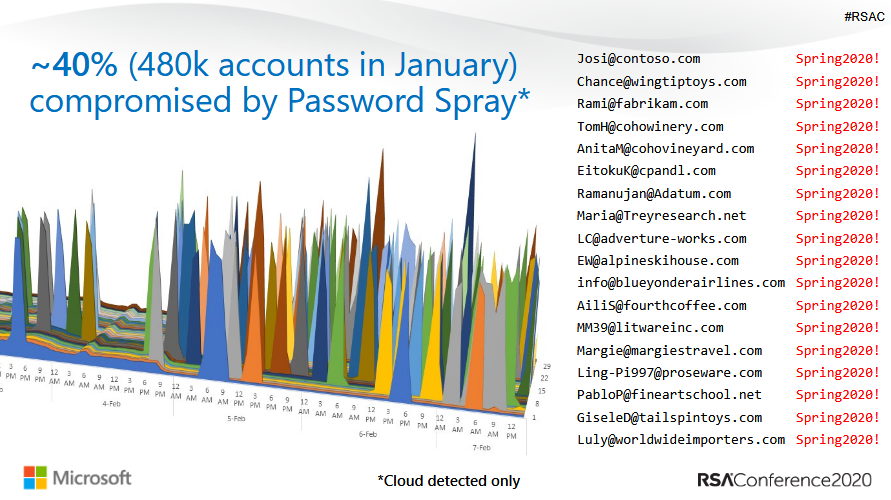
Approximately 40% of hacked Microsoft accounts in January were compromised using password spraying.
The second-most common way that Microsoft accounts get hacked is a method called password replays. This is when a hacker snatches leaked credentials from another company and then tries it on a Microsoft account.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
Unfortunately, there's a chance that the cybercriminal may find a match.
"We know that 60% of users reuse passwords. It's super common," Weinert said. "Don't be confused. People reuse their enterprise accounts in non-enterprise environments."
The vast majority of password spraying (99%) and password replay attacks (97%) that take place at Microsoft are followed through legacy authentication protocols, including SMTP, IMAP and POP.
"The reason, according to the cloud giant, is that these legacy authentication protocols don't support MFA solutions, making them ideal for hackers," ZDNet wrote.
Companies that disable legacy authentication protocols have seen a 67% reduction in account hacks.
The moral of the story here is clear: Turn on multi-step authentication for your accounts and don't be dependent on one password for all your logins.
Microsoft revealed their findings last week at the RSA security conference, an annual symposium that addresses cybersecurity concerns.
Kimberly Gedeon, holding a Master's degree in International Journalism, launched her career as a journalist for MadameNoire's business beat in 2013. She loved translating stuffy stories about the economy, personal finance and investing into digestible, easy-to-understand, entertaining stories for young women of color. During her time on the business beat, she discovered her passion for tech as she dove into articles about tech entrepreneurship, the Consumer Electronics Show (CES) and the latest tablets. After eight years of freelancing, dabbling in a myriad of beats, she's finally found a home at Laptop Mag that accepts her as the crypto-addicted, virtual reality-loving, investing-focused, tech-fascinated nerd she is. Woot!


