Ex-Hacker Dishes on New Book and How to Protect Yourself from Cybercrime
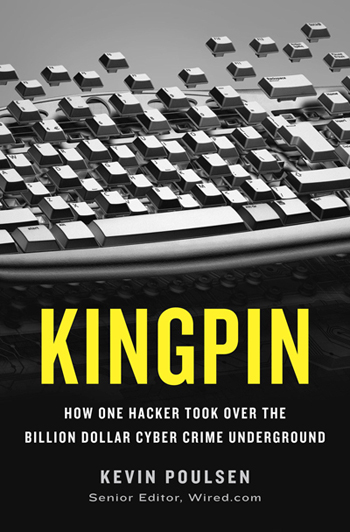
In Kingpin, Wired senior editor Kevin Poulsen follows the true story of Max Butler (Max Vision), a talented hacker who turned to the dark side of the law by becoming a major figure in the cybercrime industry. The story begins in Idaho, where Butler took an early interest in computers, and soon moves to San Francisco, where he set up shop as a white hat hacker but quickly drifts to cyber crime after a prison sentence for hacking the Pentagon and other major websites .
In 2007, Butler was arrested and sentenced to 13 years in federal prison for operating Carders Market, a popular online forum for cyber criminals looking to buy and sell stolen credit card numbers and other sensitive data. We caught up with Poulsen to get his take on the state of cyber crime.
LAPTOP: What’s the difference between a white hat hacker and a black hat hacker?
Kevin Poulsen: A white hat hacker is, for the most part, a law-abiding person who uses a hacker-like mindset to find security vulnerabilities and get them fixed. A black hat is somebody who finds security vulnerabilities and exploits them—or even somebody who takes a security vulnerability discovered by white hats and uses it criminally.
L: Are there sufficient opportunities for hackers on the white hat side of the law?
KP: Unless you have a felony conviction in the U.S. as a hacker—if you got busted as a kid or something—there’s ample opportunity to make a living as a white hat hacker in the U.S.
Overseas, it can be different. There are far fewer opportunities, say, in Eastern Europe. And it looks like that’s a big part of what’s driving the global cybercrime wave. You have people with a lot of skills, and in some cases a lot of education, who really have no way to make real money using those skills legitimately, at least if they want to be a hacker. So they’re getting into crime, and there’s a whole culture where hackers are encouraging each other to do this and recruiting each other and working together in Eastern Europe. For a long time, you could do it with relative impunity in Russia and the Ukraine. It was very hard to get busted doing this because there wasn’t a lot of police action. That looks like it’s changing, particularly in Russia, but it’s changing slowly.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
L: You have a background in hacking and were even pursued by the FBI for taking over Los Angeles’ telephone lines. How does the story of Max Vision compare to your experience in the cyber crime world?
KP: One of the things that appealed to me about Max’s story is the fact that he became a more serious criminal while he was doing time. He was in for an attack on the Pentagon, and that’s when he started mixing with serious career criminals. I saw the same thing while I was inside. When you start doing time, especially federal time, where the other inmates are very smart and they’ve done some great capers in the past, it’s kind of like joining a think tank. So you start scheming. You have opportunities and you can make contacts.
In my case, I went another way when I got out. I decided—what’s the one thing worse than being a convicted felon?—and I became a journalist. But Max obviously fell into that temptation. He had serious economic problems when he got out. So that was part of what drew me to his story. He went down a path that I could have easily gone down myself.
L: Could you explain some of the security vulnerabilities that Max and other hackers took advantage of?
KP: The SQL injection vulnerability was a huge problem at the time when Max was hacking, and he was not even the most significant exploiter of them. It continues to be a problem today. It’s one of the signature security holes of the decade, really. It’s relatively simple to combat, but a lot of companies just haven’t been doing it. Other hackers used it to perpetrate some of the largest cyber-thefts in history—stealing credit card numbers from larger eCommerce companies.
Basically, every complex website has two large pieces. One is the front end that you see when you connect to the website, and the other is on the backside. It’s largely invisible to you, and that’s the database. The website’s front end communicates with the database using this language called SQL—Structured Query Language. It’s a standardized way for a computer program to talk to the database server and to say, “give me the following data,” or “update the following data with the following values.” It’s a very, very efficient model.
The problem is that it’s all too often easy to sneak an SQL command through the website to the database server. That lets you manipulate the database to varying degrees and, in the worst case scenario, you can get it to do whatever you want. And this is something the consumer can do nothing about, and this is the salient characteristic of the hack attacks we’ve been seeing in recent years—the big ones that effect millions of people. It’s all in the hands of large companies that have insufficiently protected your data that they store for you.
L: Is this the case for the majority of people who suffer from identity theft or get hacked?
KP: Yes, until recently. There’s been a shift, where instead of these breaches at banks and retailers, the pendulum is starting to swing back the other way. The big thing now is a whole suite of Trojan horse programs that hackers are using to get control of your computer, particularly if you run a small business. Once they get control of your PC, they intercept your password or other credentials as you log into your online banking. And then they use that to siphon money from your bank account.
L: And in that case also, is there nothing you can do?
KP: There you can do something about it, although the hackers are so sophisticated that it can take extraordinary measures to really be safe. As a baseline, you should be running anti-virus software, and you should be extremely suspicious of anything that you’re not expecting that comes into your inbox. E-mail is still the primary way of hooking people with this trap. If you want to be very safe, some experts recommend that you have a computer set aside just for your online banking that you use for nothing else, and that minimizes your risk a great deal, especially if it’s running Linux instead of Windows, because the attacks are primarily targeting Windows computers.
L: How has the world of cyber theft changed in the few years since the events in your book took place?
KP: There was a real bloodletting after Max Vision and Albert Gonzalez—the TJX hacker—were busted. There was a reckoning where all of these retailers and banking card processing companies with poor security had to answer for it. Max Vision and Albert Gonzalez were part of the wave that caught everyone by surprise. Now everybody knows. All the major retailers know, but if it happens to them again, there’s no excuse for it.
What Max specialized in was hitting small, brick-and-mortar outlets, particularly restaurants. That, actually, oddly, is still going on and seems to be increasing. We’re seeing a lot of cases like that, and nobody’s really connecting the dots. If you’re scouring Google News, you’ll see that these cases are happening all the time, but they’re always local news stories. So going after small retailers keeps any of these breaches from becoming major federal investigations. But if you get a lot of these, a lot of restaurants, you can get a good supply of dumps—aka credit card mag stripe data. It’s almost like Max was the first to realize that this vulnerability existed. Now he’s out of the picture, but there are others, particularly in Eastern Europe, who are seizing on that and really just going hog wild with it.
Thank you to Kevin Poulsen for speaking with us about his new book. Kingpin is available starting today on Crown Press.