Nasty Windows printer bug lets hackers lock you out of your PC — what to do
The critical security flaw is aptly called PrintNightmare
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
You are now subscribed
Your newsletter sign-up was successful
A nasty Windows exploit was discovered within the Windows Print Spooler Service, a program that helps PCs interact with printers. Dubbed PrintNightmare, the critical security flaw allows hackers to remotely execute malicious code that could wreak havoc on your PC.
Microsoft announced that it is aware of the Printer Spooler vulnerability; the Redmond-based tech giant is currently investigating the issue and it's working on a fix to patch the security flaw.
- Windows 11 guide: Release date, beta download, features and more
- Windows 11 new startup sound got leaked — and it sounds like Minecraft music
- Best laptops of 2020
The PrintNightmare exploit affects all Windows users
The Sangfor security researchers who discovered the PrintNightmare exploit accidentally made it public before their planned release date; they were poised to unveil the vulnerability at the annual Black Hat security conference in late July. They pulled it down, but not before GitHub got a hold of it, according to The Verge.
No one is safe from the Printer Spooler security flaw. PrintNightmare, a remote-code execution (RCE) vulnerability, impacts all versions of Windows.
"An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges," Microsoft said. "An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights."
In other words, a hacker who decides to take advantage of the PrintNightmare exploit could obtain full admin rights to wipe out your personal data — and even create a new user login to lock you out of your own PC. Yeah, it's that bad.
The Print Spooler service is on by default on Windows, so the vulnerability risk for Windows users is significant. Microsoft hasn't released a patch for this critical security flaw yet, but the Redmond-based tech giant is urgently encouraging all users to update their Windows PCs.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
Workaround solution for PrintNightmare security exploit
While Microsoft works on a patch for the PrintNightmare exploit, there is a workaround solution you can employ to mitigate your risk. Since this is a security flaw that affects the Windows Print Spooler program, you can disable the service, but keep in mind that you won't be able to order print jobs to your printer with this option off.
How to disable Windows Print Spooler Service
1. Click on Start.
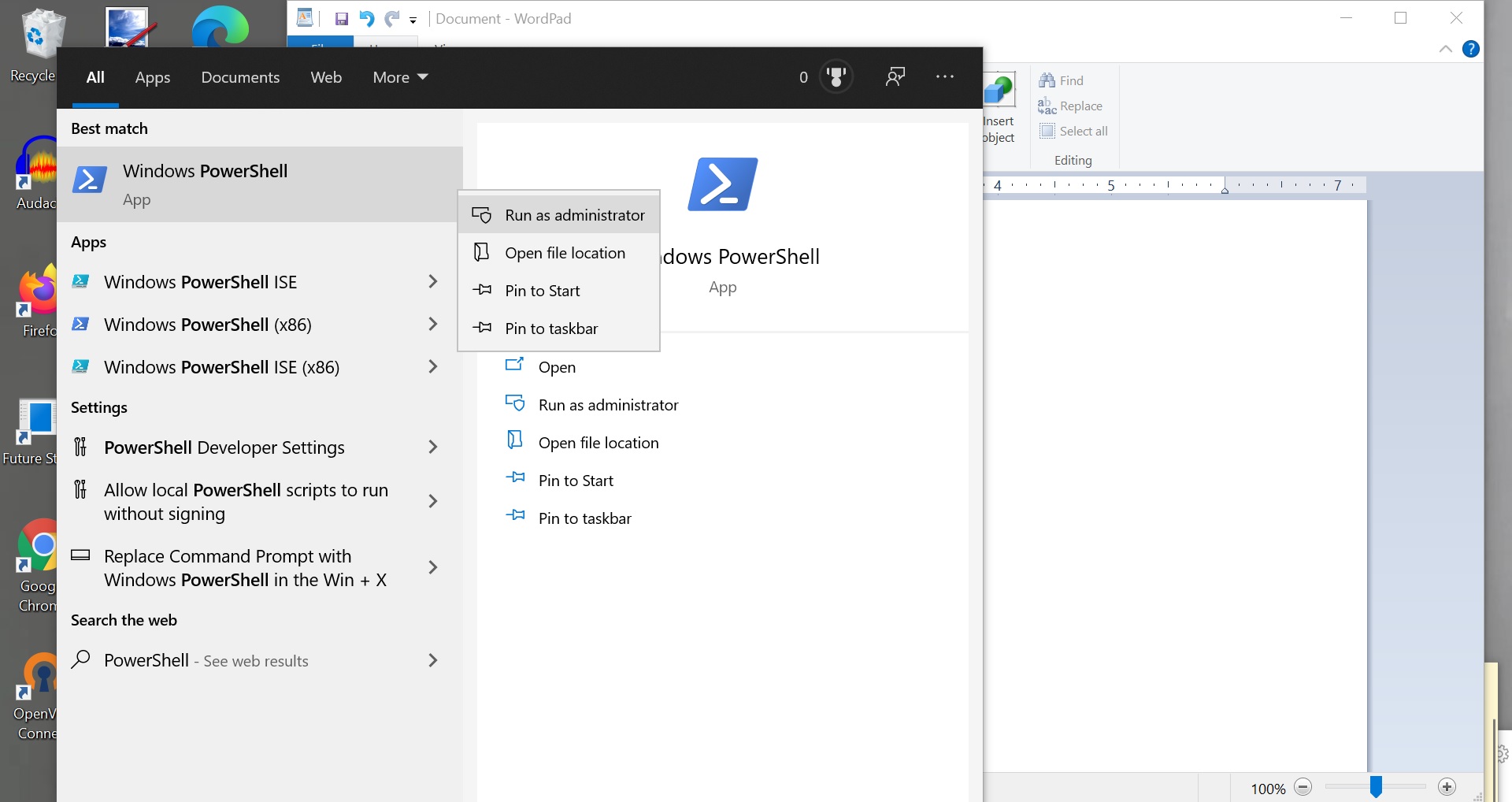
2. Type in "PowerShell." Right-click the top result (i.e. Windows PowerShell) and click on "Run as Administrator."
3. Type in the following command (this will disable the Print Spooler Service): "Stop-Service -Name Spooler -Force"
4. Type in the following command (this will block Printer Spooler Service from starting back up again during restart): "Set-Service -Name Spooler -StartupType Disabled"
5. Hit "Enter."
If disabling Print Spooler Service too inconvenient for you, there is another solution. You can block hackers from remotely accessing your PC via Print Spooler Service sans thwarting your printing capabilities. You can do this by editing Group Policy on your PC.
How to protect yourself from PrintNightmare via Group Policy
1. Click on Start.
2. Type in "Edit Group Policy."
3. Navigate to Computer Configuration > Administrative Templates > Printers.
4. Under "Setting," click on "Allow Print Spooler to accept client connections."
5. Click on "Disabled" followed by "Apply" and "OK."
6. Check that it says "Disabled" under "State" for the "Allow Print Spooler to accept client connections" option.
Now, you should be safe from malicious actors who could potentially exploit the Print Spooler Service to invade your PC.
Kimberly Gedeon, holding a Master's degree in International Journalism, launched her career as a journalist for MadameNoire's business beat in 2013. She loved translating stuffy stories about the economy, personal finance and investing into digestible, easy-to-understand, entertaining stories for young women of color. During her time on the business beat, she discovered her passion for tech as she dove into articles about tech entrepreneurship, the Consumer Electronics Show (CES) and the latest tablets. After eight years of freelancing, dabbling in a myriad of beats, she's finally found a home at Laptop Mag that accepts her as the crypto-addicted, virtual reality-loving, investing-focused, tech-fascinated nerd she is. Woot!

