This macOS malware sneakily uses devices to make money for hackers — only worry if you do THIS
This macOS malware makes money on hackers' behalf

A family of macOS malware is resurfacing to wreak havoc on users' device, according to Jamf Threat Labs team. If you're thinking, "I've got nothing to worry about! I have malware protection," I'd think twice. According to cybersecurity researchers, this particular malware sample is "largely undetected."
Investigators discovered the malware inside popular Apple apps, including Final Cut Pro, but because this version of the software was discovered outside of a legitimate, trusted source for macOS downloads, you needn't worry too much.
Sneaky macOS malware makes a comeback
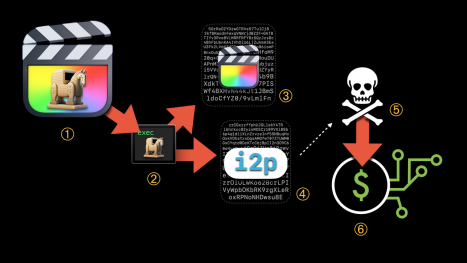
As mentioned, this malware sample discovered in modified versions of Final Cut Pro as well as Adobe Photoshop and Logic Pro X. Jamf Threat Labs team traced the source of these infected apps to a well-known piracy site often used to download popular macOS and PC software.
What happens if one of these infected apps end up on your Mac? It will use your device's CPU to sneakily mine currency for remote threat actors. In other words, hackers will take advantage of your machine's resources to make themselves money while you're none the wiser. Once the currency is mined, it will be sent to the attacker's crypto wallet.
Jamf Threat Labs admits that this malware tactic, also known as cryptojacking, is far from new, but this particular malware family uses novel tactics. "This malware makes use of the i2p (Invisible Internet Project) for communication. i2p is a private network layer that anonymizes traffic, making it a less noticeable alternative to Tor," the researchers said.
The first iteration of this malware was discovered in 2019, but underwent three stages of evolution to become the monster it is today — becoming more and more undetectable over time. For example, the current-gen version of this malware can disguise malicious components as a macOS system processes.
The cybersecurity researchers acknowledged that macOS Ventura introduced security improvements that pose challenges to cryptojacking malware. For example, when the Jamf Threat Labs team attempted to launch a malicious version of Final Cut Pro, it failed to launch and they received an error message. But there's one tiny problem.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
"macOS did not prevent the miner from executing," the investigators said. "By the time the user receives the error message, the malware has already been installed." On top of that, the error message only appeared for pirated versions of Logic Pro and Final Cut Pro — infected iterations of Photoshop launched successfully on macOS Ventura 13.2 and earlier.
The moral of the story? Stay away from piracy sites and you'll be fine, but if you choose to play with fire, be prepared to get burned.
Kimberly Gedeon, holding a Master's degree in International Journalism, launched her career as a journalist for MadameNoire's business beat in 2013. She loved translating stuffy stories about the economy, personal finance and investing into digestible, easy-to-understand, entertaining stories for young women of color. During her time on the business beat, she discovered her passion for tech as she dove into articles about tech entrepreneurship, the Consumer Electronics Show (CES) and the latest tablets. After eight years of freelancing, dabbling in a myriad of beats, she's finally found a home at Laptop Mag that accepts her as the crypto-addicted, virtual reality-loving, investing-focused, tech-fascinated nerd she is. Woot!


