News
Latest News

Best laptops with CD-DVD drives in 2025
By Rami Tabari published
The best laptops with CD-DVD drives — and an alternative to consider

This is your brain on ChatGPT
By Rael Hornby published
MIT finds AI tools like ChatGPT can limit brain activity, impair memory, and decrease user engagement.

MacBook Air vs. MacBook Pro 2025: Which Mac should you buy?
By Sean Riley published
Our guide to deciding between the MacBook Air vs. MacBook Pro in 2025 is based on hundreds of hours of testing and our thorough reviews of every MacBook.

I used the Switch 2 and Switch OLED side by side for a week — here’s what surprised me
By Rami Tabari published
The Switch 2 is here, but is it really better than the Switch OLED? Let me tell you why you shouldn’t count the Switch OLED out just yet and why, depending on your needs, it might be worth upgrading.

I switched to a MacBook after using Windows for over 30 years. Here’s what happened.
By Jowi Morales published
Switching from Windows to a MacBook after 30 years showed me the way of macOS, but there's something about PCs that I just can't give up.
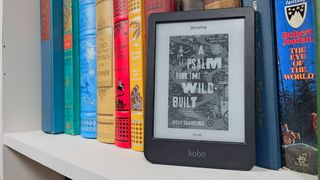
I switched from a Kindle ereader to Kobo for a week — here's why I'm never going back
By Stevie Bonifield published
I ditched my Kindle for a Kobo ereader for a week. It changed my mind about my favorite way to read ebooks.

I found 65 early Prime Day tech deals to shop now ahead of Amazon's July 8-11 sale
By Hilda Scott last updated
Shop the best Amazon Prime Day deals in July for the best summer discounts and back-to-school savings.

I tested Nvidia's DLSS Transformer Model — my games look better, and it cost me nothing
By Madeline Ricchiuto published
Better DLSS is no joke
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.


