Scammers want your stimulus check: Here’s how to stop them
Phishing attackers are capitalizing on the stimulus check roll out

Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
You are now subscribed
Your newsletter sign-up was successful
"Where's my stimulus check?" is now one of the most popular questions on Google, and if you're not careful, the answer will be, "in the hands of a cybercriminal." Cybersecurity firm Check Point Research spotted an upsurge of malicious domains targeting Americans questioning the whereabouts of their COVID-19 payment relief.
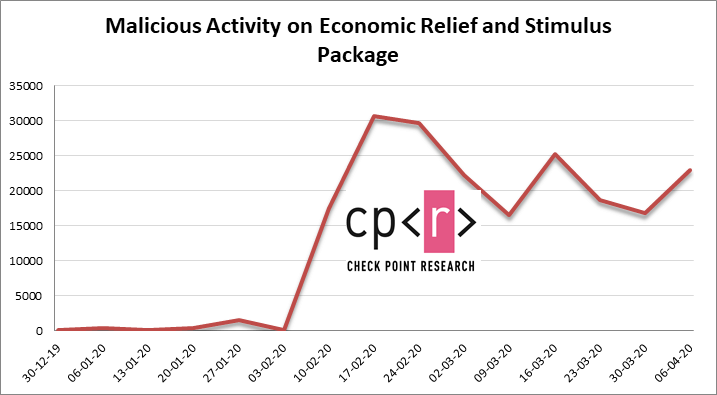
During March and the first week of April, more than 2,500 new domains related to the IRS stimulus check roll out were registered. Check Point Research spotted a massive spike during the week of March 16, when the stimulus package was initially proposed to taxpayers.
- Coronavirus is being exploited by hackers to spread malware: What to do
- Apple, Netflix among most imitated brands for 2020 phishing attacks
- 500,000 Zoom passwords sold on the dark web: Check if you're compromised
"The number of new domains registered that week was 3.5 times higher compared to the average of previous weeks," the report said.
Article continues belowOf those 2,500 new domains, more than 700 of them raised alarm bells on analysts' radar as potential cyber threats to unwitting, internet-surfing victims.
In a recent blog, Google also announced concerns about the uptick of cybercriminal activity. During the second week of April, the search-engine giant discovered more than 18 million malware and phishing emails related to COVID-19 daily -- this is on top of the daily 240 million coronavirus-related spam messages Google spotted during that same time frame.
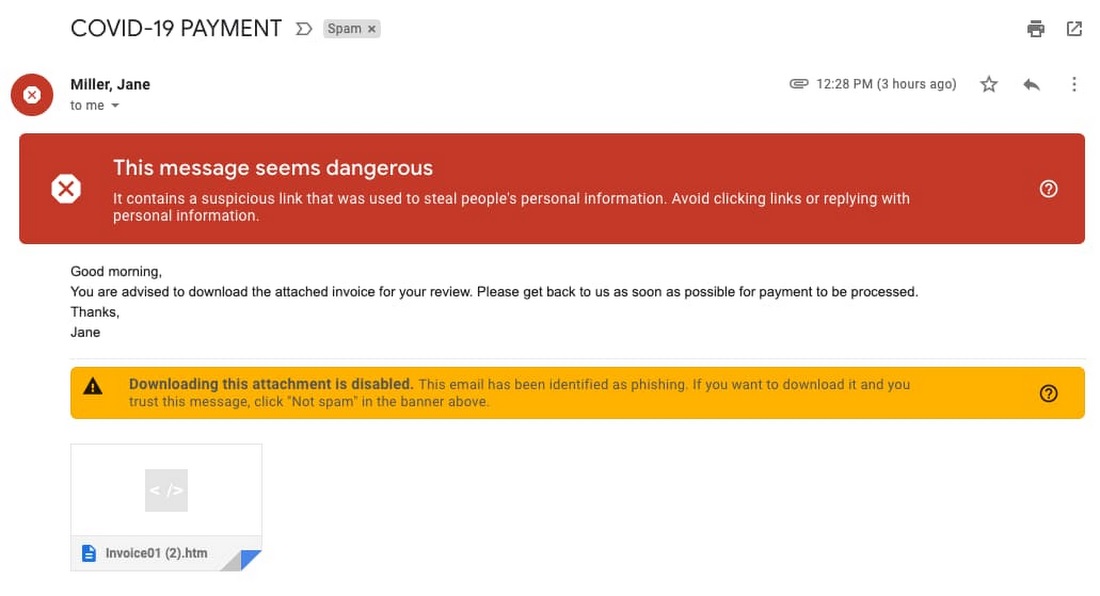
"The phishing attacks and scams we’re seeing use both fear and financial incentives to create urgency to try to prompt users to respond," Google wrote. The tech giant posted an example of a hacker capitalizing off the stimulus check roll out with an email titled, "COVID-19 Payment."
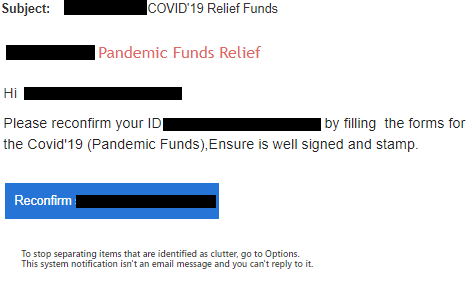
Check Point Research also posted an example of their phishing discoveries. In one email, the cybercriminal goaded an internet user to click "Reconfirm," which led him or her to a new window that prompted the disclosure of one's personal information. The cybersecurity firm found malicious threats such as AgentTesla, which is a password-stealing malware program, and Zeus Sphinx, a Trojan that's used to snatch online banking credentials.
Sign up to receive The Snapshot, a free special dispatch from Laptop Mag, in your inbox.
"These threats are not new," Google wrote. "Rather, they’re existing malware campaigns that have simply been updated to exploit the heightened attention on COVID-19." But Google assured Gmail users that its new AI malware scanners help filter out 99.9% of spam, malware and phishing attempts.
Taking the best tips from Google's recent blog and Check Point Research's report, here's how you can protect yourself from falling into a cyber-threat trap:
- Double-check suspicious attachments. Use Gmail's built-in document preview.
- Beware of spelling errors in emails or websites. This is a tell-tale sign that you're looking at a cybercriminal's bait -- do not fall for it.
- Be cautious of emails prompting you to take unusual actions. This could be a cybercriminal masquerading as a legitamate website to phish for your personal information.
- Never order goods from promotional links in emails. You're better off Googling your desired retailer and clicking the official website from the results page.
- Do not reuse the same password. If hackers get a hold of your "master key" password from one data breach, they can gain access to all your other accounts.
Google also advised users to enroll in their Advanced Protection Program (APP)— the tech giant claims that everyone who's participated in the program has never been successfully phished, even if they've been repeatedly targeted.
Kimberly Gedeon, holding a Master's degree in International Journalism, launched her career as a journalist for MadameNoire's business beat in 2013. She loved translating stuffy stories about the economy, personal finance and investing into digestible, easy-to-understand, entertaining stories for young women of color. During her time on the business beat, she discovered her passion for tech as she dove into articles about tech entrepreneurship, the Consumer Electronics Show (CES) and the latest tablets. After eight years of freelancing, dabbling in a myriad of beats, she's finally found a home at Laptop Mag that accepts her as the crypto-addicted, virtual reality-loving, investing-focused, tech-fascinated nerd she is. Woot!

